Friday's attack on the internet is a watershed event in the chronical of national security and economic stability. Mark the moment, we've witnessed the Democratization of Global Power.
Here's why.
But first:
What is a DDoS Attack?
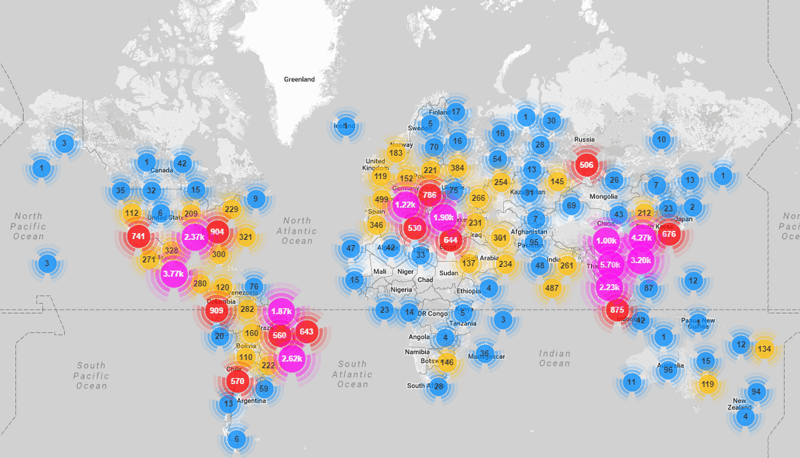
Much of the world's internet, 177 countries by one researcher's observation, was brought to its knees on Friday by a Distributed Denial of Service attack - DDoS.
The DDoS method of attack applies electronic brute force to a targeted computer using other computers infected with malware to make the assault - typically personal computers owned by individuals that are entirely unaware their devices are under the control of a malicious party that could be anywhere in the world.
These "zombie" computers barrage the target with enough spam traffic to collapse its operation and take it offline.
Video illustrating a DDoS attack:
So, who inflicts DDoS attacks, and why?
Who Does It, and Why?
 Some hackers flex their power to control distant systems just for the notoriety and acclaim it brings in their circles.
Some hackers flex their power to control distant systems just for the notoriety and acclaim it brings in their circles.
Over the past several years, DDoS attacks are increasingly being used as an extortion tool for criminal profit. Organizations and enterprises are forced to pay a bounty to get their systems back online and back in business.
Sometimes a DDoS attack is used as a distraction - a principal in the Art of War. Center attention on one thing, while you are doing another.
More recently certain DDoS attacks have been looking like political actors testing system resiliency and the method's potential to inflict influence from the outside. The goal is to exert will and execute on an agenda from a distance - no physical or material presence required.
"Zombie" computers comprise the troops, and the ammunition is electrons traveling the globe's fabric of the world-wide network.
It makes one wonder, "What would Napoleon Do?" to command strategy in the Digital Age.
What's Makes Friday's Attack So Different?
We believe Friday's attack marks an important moment in the history of national security and economic stability.
Global power has just evidenced a seismic shift - and that the notion of everyday risk at both the institutional and individual levels, from the public sector to the private sector, will never be the same.
The Democratization of Global Power.
That's a big idea, and here's why:
#1 - The Scale of the Attack
Friday's DDoS attack was massive and reached almost every country in the world because here it wasn't inflicted with a specific target in mind.
Instead, the aim of this assault was to disable a component of the internet's backbone to bring down much more than a single operator. As a result, widespread outages were experienced at some of the internet's largest websites such as Twitter, Amazon, Box, and many, many others - including the Department of Justice.
The above chart by Imperva is a snapshot of the activity representing the 177 countries invaded by Friday's single DDoS attack. It's a global blitzkrieg without a defense and not a plan in sight.
#2 - The Attack Was Distributed Using the IoT - Internet of Things.
We regularly speak around the country on cyber risk and cybercrime. Our audiences represent diverse groups from "the boardroom to the break room," and include individuals with a broad range of technical sophistication.
Over the course of the program, several questions are asked of the groups as a gauge of awareness and fluency in the subject matter. One question that typically gets very few, if any response other than a sideways glance or two, is: "Who knows what the Internet of Things is?"
Anyone?
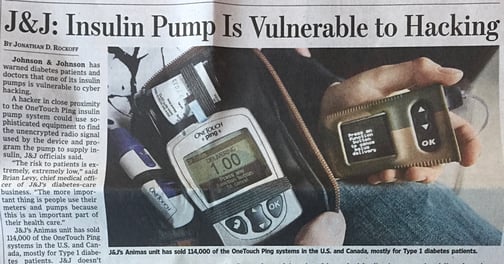
The IoT or Internet of Things is a term describing electronic consumer products that operate with computer chips and internet connectivity - like Smart TVs, security cameras, DVRs, and more recently: cars, medical devices, and even home appliances.
It's widely expected by 2020 the world will have 20-50 billion of these "smart," "aware," and internet connected "things."
20 to 50 Billion Internet Connected "Things" by 2020.
Friday's DDoS attack used the IoT to distribute the strike to the target.
Instead of an army of "zombie" computers, or "bots" that have traditionally been chained as slaves to perpetrate the assault, a massive number of "things" stormed a vital piece of the web to cause global outages and ensuing disruption.
Now, the attack surface for hackers whomever they are and regardless of their agenda has just increased exponentially and has super-charged their power to disable the internet with the click of a mouse-button from anywhere in the world.
It's estimated Friday's attack was perpetrated using 10's of millions of these "things" which are vastly unprotected (unlike some computers with firewalls, and antivirus defenses.) And, these devices usually do not have a password reset that would otherwise disconnect them from the attack and allow them to resume normal operation. To take one of these devices offline and disable it from participating in the attack requires unplugging it and putting it out of commission.
#3 - Anyone Can Do It
The source-code for the software, called "Mirai", was first used just a few weeks ago by a group of hackers against cybersecurity-guru Brian Krebs. Their goal was retaliation for his efforts to inform the world of the escalating risks we face in the cyber-sphere. Krebs appropriately called it "The Democratization of Censorship." Ponder that one for a moment - deeply scary stuff.
Well, the Mirai source-code was shortly thereafter released online and made available to anyone. For free. And it requires little expertise - no coding skills or computer science degree needed. Now, anyone can be the general in an army of millions in the quest to further their agenda, whatever it may be - criminal, political, military, mischief, ... boredom ... pick your gripe and click "Charge!"
What Now?
So, now that world has changed, "What now?"
We have a lot to say in reply, and have said a lot about it over the past four years or so, but will be giving our answers in direct response to Friday's incident later this week.
In the meantime, think "Gathering Hordes" and "Cadre-Militia" for a sense of the global challenges immediately ahead.
To stay up to date, you can subscribe here:
http://www.totaldigitalsecurity.com/subscribe-to-the-cyber-advisor-letter
Additional recommended reading on the matter: Krebs on Security
https://krebsonsecurity.com/2016/10/hacked-cameras-dvrs-powered-todays-massive-internet-outage/
How to Prepare for the Digital Age?
https://www.totaldigitalsecurity.com/the-four-fundamentals-of-cyber-security-for-life