3 min read
Let's Talk Mobile
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...

Last year China demanded Apple stop selling VPNs. Then they outlawed encryption. Now, it's Russia doing the same. VPNs are the great equalizer in the Digital Age. VPNs democratize privacy and digital freedom. In the Digital Age, VPNs are as threatening to big government as guns and gold.

"When big government starts taking, it's time to start getting."
Like guns and gold, personal information and privacy are among today's tools of power and wealth. Now, like traditional targets of individual freedoms, they too are under assault and the stakes are just as high.
This isn't a political forum, and Total Digital Security isn't engaged in the practice of politics. But we believe in the right to privacy, and that privacy is fundamental to democracy. And, we're driven by the notion that digital autonomy is increasingly vital to self-preservation for individuals and families.
But mostly, we're pragmatists that work in the field of personal cybersecurity.
Individuals, families, professionals; people that want to protect their mainstream lives use our services to protect from cyber risk and control their digital footprint as much as they can.
So, when big government and big business align to take away personal rights, reduce digital autonomy for individuals, and increase the level of cyber risk in our daily, mainstream lives, it gets our attention.
Our (pragmatic) response:
Using the internet makes you naked for all to see.
Using a VPN when on the internet makes you invisible. Like a ghost floating about the vast World Wide Web.
The magic is in the VPN's application of encryption. When a VPN encrypts the user's online connection it protects her identity, location, activities, and intentions. All are private and under the user's control.
Online banking, shopping, browsing, passwords, email - with a VPN it's encrypted and invisible, except to your final digital recipient.
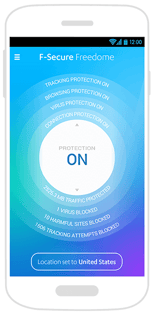
Not many years ago VPNs were still prohibitively expensive. They required lots of hardware and were exceedingly difficult to use, especially with a mobile device. Now, VPNs comes in the form of an app.
They're affordable to most, made of software, and simple enough for personal, everyday use. The only requirement from the VPN user is to keep the app "On" and perhaps change the server location when traveling abroad.
Through the application of encryption when online, VPNs deter cybercrime, reduce the user's digital footprint, and increase information privacy and control.
See above.
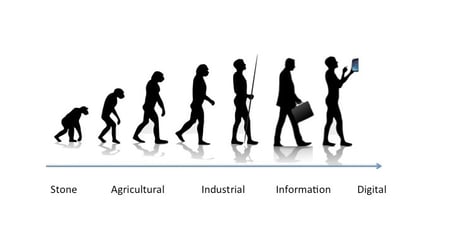
VPN technology is democratizing encryption, and encryption is a powerful tool for personal autonomy and freedom in the digital age.
Like guns and gold.

The magic of a VPN is in its application of encryption. And it's encryption that is the actual target of Apple and China's censorship.
Encryption jumbles and scrambles information making it unreadable without the keys to decrypt. Digital encryption today uses big math and significant computational power to create codes that are infinitely complex and secure. A VPN is the software vessel for which your online communications are encrypted from the point of leaving your internet-connected device to its intended digital recipient.
In the digital age, encryption empowers individual freedom and autonomy. Like guns and gold, individual ownership and control of personal information is viewed as a primary threat to those bent on political control and economic manipulation.
Your survival and success in the digital age depend on encryption. One day not far from now, a personal encryption code will be the master key to all of your kingdom. We recommend taking every opportunity to learn about encryption, how to apply it with control to all aspects of your cyber-life, and to start getting comfortable demanding the keys to your digital self.
A VPN is an ideal method of introducing encryption to your everyday life. Using one on your smartphone deters most cybercrime like ID theft, online fraud, financial scams and the other digital crimes that are increasingly the target for all professional criminals around the world.
But most importantly - using a VPN prepares and positions you to benefit from the great innovation in encryption technology that is currently underhand.
Not using a VPN and encryption gives all the advantage of evolvement and adaptation to those that would do you most harm.
Here is an explanation and image of a VPN and encryption:
"Using a VPN - the before-and-after."
Maybe you've heard - choosing a VPN is tricky.
Some actually look for "free" VPNs. Not wise. Just search "VPN fraud" to see why.
Many factors come to play when choosing the right VPN for you:
Geography?
Yes, geography.
The law of the land rules all and the location of a VPN provider can mean everything to the integrity of the operation. The country's constitution and its protection of individual rights, the government's history of warrantless activity, cultural attitudes toward privacy; all should be evaluated when choosing the right VPN provider for you.
BOTTOM LINE - the best technology and protection is no match for a government set against individual freedoms and the liberty to choose.
In the end, it's important to consider geography when evaluating anything relating to digital security.
Total Digital Security finds the best IT security technology available to anyone, anywhere, and makes it accessible, affordable, and easy to use for the rest of us.
We have years of experience evaluating products, services, operators, and sovereign jurisdictions as they apply to cybersecurity and digital autonomy for individuals and small groups.
For more on the VPN we recommend, and how to get it:
It's what we do.

3 min read
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...

5 min read
A massive cyberattack made headlines — and the weapons it used might be sitting in your home or office right now.

5 min read
In our last post, we introduced the three primary attack surfaces every family needs to understand: email, devices, and networks. Today we're going...