3 min read
Let's Talk Mobile
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...

When using your phone to connect to a public WiFi hotspot, the signal from your device to the WiFi router is easily tapped, monitored, and scanned using cheap, widely available technology. Anyone can do it. Also, without protection, your phone can be "hijacked", held for ransom, and all of the information held on your phone is open to loss and theft. Financial fraud, ID theft, and ransomware over WiFi is becoming as common as any petty street crime and is being compared to the Digital Age's version of a modern pickpocket. Fortunately, advanced IT security technology has become easy to use and affordable, and now anyone can become virtually invisible on WiFis and the internet by using a VPN.
My job writing this blog is to inform, educate, and connect individuals, families, professionals, and small businesses with the best IT security products that are available to anyone, anywhere.
And my company, Total Digital Security, makes these commercial-class technologies accessible, easy to use, and affordable to my readers and our customers and personal VPN services.
The VPN is a prime example in that it is highly sophisticated technology once used only by leading edge, mission-critical operators. Now, after years of development and innovative advances in hardware and software tehnology the highest quality VPN's are suitable and affordable for markets as small as one. Considering the increasing risks of loss from cyber crime, and the low cost for serious protection from a VPN, it's an easy conclusion. An added bonus to using a VPN is the sense of empowerment that comes with it - you are reclaiming control of your surroundings and protected from harm.
The signals moving outbound from your phone or device over WiFi? They're encrypted. A VPN automatically encrypts all of your online activities - passwords, shopping, banking, email, all of it is encrypted and unreadable to anyone from the outside. Then, all of your online traffic is tunneled over private servers - off the grid of the "public" internet.
With a VPN, your are virtually invisible online.
Let's use a public WiFi as an example. The images are "before" using a VPN, and "after" using a VPN.
 Before Using a VPN.
Before Using a VPN.
 After Using a VPN.
After Using a VPN.
Before VPN
The man on the left is connected to a public WiFi in a busy, public space. In the "before" image, everything he does is available to anyone to see. The hacker on the right is collecting passwords to your most sensitive accounts, going into your bank accounts, perhaps if you are a professional advisor - even viewing confidential client information. The hacker can seize control of your information, send it off to a remote location, and lock it up for a ransom payment. Without a VPN, you are entirely exposed and vulnerable.
After VPN
Now, the wireless information is encrypted, invisible to the outside, and the hacker is locked out, to move on to the next victim.
A VPN also protects when your internet activities move past the local WiFi network, and on to the main network of the internet. Instead of your information traveling over the public grid of the internet's plumbing, with a VPN it is "tunneled" through the public grid on private servers that are protected from the hostilities online.
VPN - A Cloak of Invisibility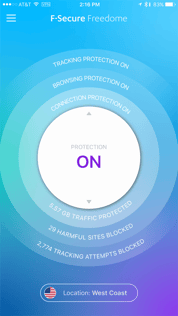
The Bottom Line - We have written extensively on VPN's; how they work, why to use one, and which is best, and a Google search will give you all the details you need so we won't go in to it here - but, think of a VPN as a cloak of invisibility. Turn it "on" and everything you do online is invisible to the outside.
Our recommendation - it's simple - use a high-quality one every day and don't leave home without it switched "on".
Start using one now to reduce your digital footprint, and use the internet with confidence that you are protecting your information; your location is private, and you are safe and secure from the rapid increase of threats online.
With a VPN, you get what you pay for, and we warn away from many of them. Some are scams and used as honey-pots for information aggregation. Many are clunky to use and require too much fiddling with on a regular basis for most users.
Our approach is to find the best IT security solutions that are available, not watered down retail substitutes for the real thing, and bring them to our distinct markets: individuals, families, professionals, and small businesses.
For VPN's, our preferred provider at this time is F-Secure and their "Business Advanced" version of their world-class VPN: "Freedome." You can't get this commercial-class VPN service on the App or Play Stores, but you can access it uniquely through Total Digital Security.

3 min read
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...

5 min read
A massive cyberattack made headlines — and the weapons it used might be sitting in your home or office right now.

5 min read
In our last post, we introduced the three primary attack surfaces every family needs to understand: email, devices, and networks. Today we're going...