3 min read
Let's Talk Mobile
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...
I tell people being in the cybersecurity business is a front-row seat for what’s really happening in the world of hacking and cybercrime. Especially the way we operate. Our customers are people, not IT departments and servers, and we see a fundamental shift in cyber risk in our daily lives.
For us, the operating arena isn't about servers, LAN cables, and databases. But is about Windows, Macs, Androids, Apple iPhones and iPads, and the people that own and use them throughout their lives, personally and professionally. Our customers are individuals, families, small business operators; people that use personal technology and the internet to enhance their daily activities and experiences. Our field is where the rubber hits the road in cyber threats today, and as a result, we have a distinct finger on the pulse of what hackers are doing and where the action is heading.
Since the second half of 2017, we see a continuation of a trend that is now accelerating and gaining traction as we enter the second quarter of 2018.
More on the developing trend later but first some context.
Before starting Total Digital Security in 2013, I had spent the previous 25 years advising some of the wealthiest families in the world. I was an executive with Wall Street’s most prestigious banks. For my ultra-wealthy clients and me; it was all about risk - risk awareness and understanding, and risk management and mitigation. We were relentless in asking ourselves; what could go wrong, and how do we avoid it. When facing the question in early 2012 we received a new answer, and it would soon challenge every assumption we had ever held about our job.
Here's what happened.
During the first decade of the 2000's the internet's "democratizing" effect began pushing cyber-risk downstream to include not only big governments, militaries, and Fortune 500 companies, but also new targets like mid-sized companies. And, the attacks and incident rates evidenced more than the traditional sort of cyber-espionage, theft of intellectual property, and political 'hacktivism,' Increasingly, the hackers' goal was financial gain.
Then, around 2010, the ubiquity of internet-connected smartphones and information-rich 'clouds' drove cyber risk further downstream to include smaller targets. The new cybercrime-for-profit attacks included small businesses and professional practices; law firms, CPA's, small investment firms, and healthcare companies, as examples.
In another marker of change, in these cases, the perpetrators weren't only pimple-faced teens and black-hats, but increasingly included professional criminals and amateur wannabe's. Now, cybercrime was becoming job #1 for traditional crime cartels, newly organized hacking syndicates and even disaffected street thugs from around the world.
By this time, the downstream pattern was evident, at least it is in retrospect, but by 2012 the next stop for cybercriminals was the rich, powerful, and famous. Now, the hackers were aiming for my clients; the uber-wealthy, and the personal technology they used every day.
It was shocking at the time, how quickly it happened. But from a slow start in the 2000's, by 2013 cybercrime-for-profit accounted for more than half of all cyber attacks around the world. Now, I understood and could see how it would play out. Cyber risk would eventually migrate to very last capillary of the internet; the individual user and their internet connected devices.
And, by my reckoning, it would get there before the end of the decade in 2020.
The pattern continued, and by 2016 law enforcement in the U.K. declared cybercrime accounted for more than half of all crime in the country. Then in 2017, at Warren Buffet's annual Berkshire shareholder love-fest in Omaha, when asked about risk in the world he replied: "Cyber, it's the #1 problem for mankind." Mr. Buffet went on to clarify; in his view, cyber risk posed a greater threat to man than nuclear and biological.
If that doesn't punctuate the internet's democratizing effect on cyber risk, I'm not sure what does.
So, let's get back to the previously mentioned trends we see from late 2017 and into 2018. Well, if you extrapolate the patterns we discuss in our experiences and observations, including direct from the field between 2012 to today, it's not entirely shocking; cyber risk continues to move downstream.
Today, cybercriminals are targeting broader economic classes and aiming at the mass-affluent and upper-middle-class. In the business sectors, targets continue to move downstream in size, and attackers are agnostic to the industry served. Now, if you engage with information and technology, you are a target of cybercriminals from around the world.
Here's what that looks like in the real world and a sampling of recent cases we've handled:
It goes on.
Some stories and cases are heartbreaking.
I think you get the idea, and I don't want to dramatize or overdo the message here, but it's important to know; the potential damage is severe.
Here are five crucial takeaways from these experiences:
1. All of the breaches took place on personal technology - no servers, blades, LAN rooms, or databases involved.
2. The majority of cases begin with information stolen from computers and laptops used at home.
3. The victims, when not a small business, were affluent upper- middle-class individuals or families.
4. Three-quarters of the victims are retirees.
5. All of the exploits started with unsecured and "free" email accounts.
![]() For the couple that lost $95,000 as the buyer in a residential real estate transaction, it started with a hacked Gmail account used by the agent during sales and closing. The client’s lawyer is considering a suit against the agent and broker for not taking reasonable measures to protect the parties involved.
For the couple that lost $95,000 as the buyer in a residential real estate transaction, it started with a hacked Gmail account used by the agent during sales and closing. The client’s lawyer is considering a suit against the agent and broker for not taking reasonable measures to protect the parties involved.
![]() For the individual that lost multiple investment accounts across several firms simultaneously, we determined her email account had been hacked and the criminals were skulking her activities for at least weeks, if not month, before the breach.
For the individual that lost multiple investment accounts across several firms simultaneously, we determined her email account had been hacked and the criminals were skulking her activities for at least weeks, if not month, before the breach.
![]() The trend to steal information from home computers for hacking bank and online investment accounts is confirmed by the financial services industry for 2017. And this year the IRS has been reaching out to CPA firms warning them of hacking rings focused specifically on their practice and clients.
The trend to steal information from home computers for hacking bank and online investment accounts is confirmed by the financial services industry for 2017. And this year the IRS has been reaching out to CPA firms warning them of hacking rings focused specifically on their practice and clients.
Hacking and cybercrime are increasingly a threat to mainstream life, and it's going to get worse for at least a few more years before regulation, law enforcement, and broad adaptation measures counter the tsunami-sized wave of change and risk we have immediately at hand.
What's the good news? You can do a lot to reduce the risk.
There are a handful of disciplines and measures that provide instant risk mitigation effects, reduce your digital footprint, and over time increasingly make you less relevant to those that would do you harm online. It’s important to understand; protective technology is effective, getting better regularly, and will continue to do so rapidly into the near future.
First, be sure your network of professional advisors is taking your privacy and information security seriously. If a real estate agent, CPA, or any other "trusted client advisor" is using "free" email like Gmail, Yahoo, AOL, and the like, they are obviously not with the times. Either give them a last chance ultimatum to adapt, or probably more wisely; fire them.
If they haven’t made an effort to secure their email communications by now, you have to wonder how they view the value of your professional relationship. It’s 2018 folks – do not wait to have these conversations.
Also, as a priority for protection; privatize your email accounts.
Remember, cyber-attacks today start by targeting people, not IT departments. Privatizing email gets you off the grid of abuse and risk at “free” providers and is a fundamental adjustment. We create personal and business email domains for clients all the time and its one of the “fundamentals” we discuss in every case.
Establishing your own email domain gets you off the grid of abuse and risk at the "free" services, and ownership of your personal information will be an imperative before long. Your information’s value, especially to you, will only increase in time, as will the added digital autonomy it provides.
Learn more about private and secure email accounts here:
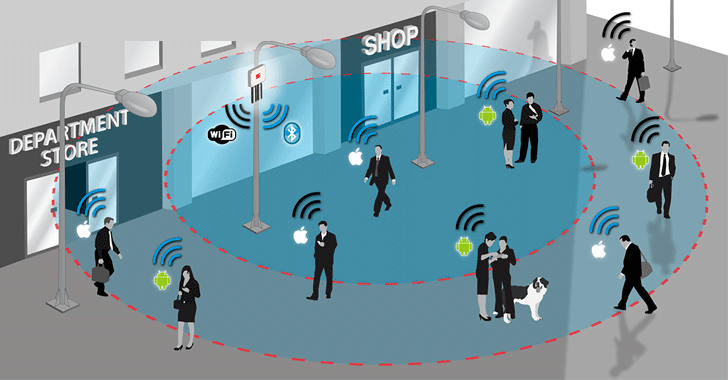
Another fundamental for risk management today; protect the home internet network and Wi-Fi. It's the port-of-entry to your life.
Take control of your network like it was the main gate to your kingdom, because in the digital age; it is. Especially with smart homes, internet-connected cameras and other "smart" devices.
There are remarkably innovative and effective solutions for fixed-networks that have evolved to plug-and-play "set-it-and-forget-it" simplicity, and yet operate with the effectiveness of "an IT security department in the basement." As we continue to emphasize; cybersecurity is big-business, and the consumer is increasingly the winner in terms of performance and value.
Click below to learn more about Router Network and WiFI Security:
From a best-practices standpoint, face it; it’s time to discipline yourself to manage passwords, use two-factor authentication, freeze credit files, use a VPN, and other measures that are inexpensive or free, and yet are extremely effective at reducing cyber risk in your daily life.
You can visit www.totaldigitalsecurity.com for everything you need around these measures.
When I think back to my days in banking, I recall when advising clients to take certain measures to reduce certain risks invariably the response would be "How much will it cost?" In other words; "what’s the risk/reward, the economic value at stake?" Answering the question regarding avoiding cyber risk is simple today; there is likely no greater economic value or more successful risk/reward analysis than that of using advanced cybersecurity technology to protect from loss and damage associated with cybercrime.
Use it and find yourself and those you care about most empowered for survival and success in the new digital age.
Contact us to learn more about protecting your business, professional practice, family and home.

3 min read
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...

5 min read
A massive cyberattack made headlines — and the weapons it used might be sitting in your home or office right now.

5 min read
In our last post, we introduced the three primary attack surfaces every family needs to understand: email, devices, and networks. Today we're going...