The Democratization of Cyber-Risk
Why You, Your Family and Small Business are the TARGET for Hackers in 2014.
The watershed event for 2013 in the world of cybercrime might just be the Black Friday Target breach. It certainly is if you put the NSA revelation by Edward Snowden aside. Regardless, they are both markers on the historical timeline of cybercrime and the emergence of large scale "horizontal" breaches in online security and privacy.
Why You Are Now The Bullseye -
In previous blogs, I've explained "vertical" breaches (the Pentagon, DropBox, LinkedIn, etc.) being those that find a single target to be of "high-value". The new wave is "horizontal" in that digital surveillance technology can now scan millions of individual targets, like you and me, and glean the data with big-data software to create a large, horizontally assembled high-value target. Snowden's expose' revealed the extent of the US government's use of this method, but we also know that corporate and criminal hackers use the same approach and have probably been empowered by the NSA's enormous investment in furthering this technology. This is the environment that is quickly democratizing cyber-risk in the world today. What's at stake are the most meaningful people and the most irreplaceable things, in our respective lives.
110 Million Bullseyes in this TARGET -
The Target breach is an example of a vertical breach with over 40 million of it's customers losing sensitive information to the attack. In many cases, another hacker will purchase credit card and PIN information to fraudulently purchase and perhaps re-sell merchandise before the system catches up with them. In these cases, the consumer is protected. This link is a good report on how they undertake this fraud once credit card numbers are in hand; What Happens When Your Credit Card Number is Stolen?
What They Do With Your Stolen Information & Why You Are Not Protected -
Now, here is where it becomes different and gets interesting. Stolen credit card numbers are nothing new, but, the ability for almost anyone to steal this many of them and then use them all as a mechanism for large-scale financial-fraud, is. The stolen information from tens of millions of Target customers will be assembled and analyzed using big-data tech and then used for a single (or more) large-scale horizontal attack that will affect many, potentially 100,000's or millions, of individuals and families. And, in this case, the credit card victim has no protection. Nobody else will stand-in and shoulder the consequences of the breach. You are individually accountable and at risk. This mass-scale horizontal attack represents the new era in cybercrime and the individual, family and small business has perhaps, at the outmost, 12 months to prepare for the decade long cyber-storm which is at hand today.
The hackers will use the details gained from the Target breach, such as credit-card numbers, PIN's, sign-on's, etc., and overlay other metadata they have collected from scanning Gmail, Yahoo, AOL and other large providers of "free" email (just as the NSA does), analyze it all with big-data software and aggregate those where they have discovered enough variables about you to crack the code of your online security. This may end up in socially-engineered emails and in ransomware attacks where your life's worth of data is held hostage. Social engineering, an outstanding piece from Kaspersky Labs;
http://blog.kaspersky.com/social-engineering-hacking-the-human-os/
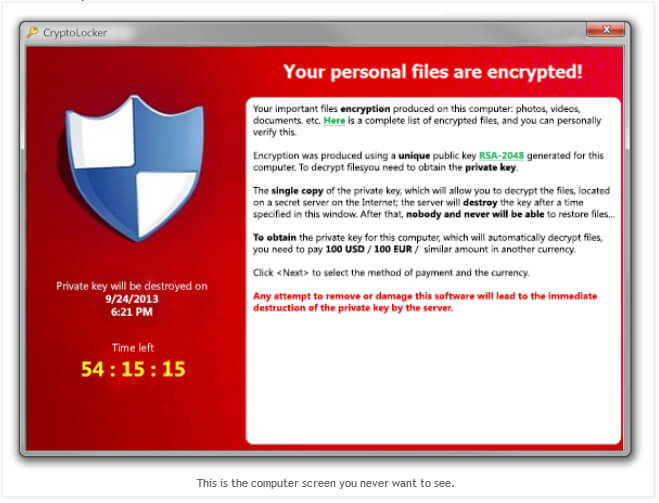
Ransomware And Why This is The Last Computer Screen You Ever Want to See -
What is Ransomware?
Ransomware is the evolution of extortion. Only the booty and means to the crime have changed.
What is Ransomware?
Is ransomware "the" word for 2014 in cyber-crime?
Ransomware on the Increase in 2014.
What Happens in a Ransomware Attack.?
Ransomware is the hijacking of your digital life. All of your data is encrypted and held for ransom. Typically the amount is not insurmountable but, you only have a brief period of time to fulfill the demand. The hackers are counting on you and millions of other victims in the attack to just pay-up and be done with it. In many cases, unfortunately, this is the least damaging of all outcomes.
What Does One do to Protect Their Homes and Families from These Risks?
Hackers have excelled at leveraging the exponential gains in technology to their personal advantage. Furthering their innovation has been the institutional targets which have spent decades and billions in order to protect themselves. This tension between the two has created an arena of very robust tools for attack, and defenses to protect. Until now these tools of attack have been oriented to the server environment of the institution and not necessarily toward the individual end users that reside at the capillaries of the internet. The good news is that we can now use the same technology the institutions have developed for their defense, for the sake of our own. Without enterprise-grade defenses, individual users of the internet have little, if any, chance of surviving in light of the new era of cyber-crime.
To be smart and strategic in the new environment it's helpful to understand a very core concept which holds the key to understanding what lies ahead. Albert Einstein, Carl Sagan, and many others scientists have said that the understanding of this concept is crucial to a general understanding of the way things simply work, anywhere in the universe.
"If you understand exponentials, the key to many of the secrets of the Universe is in your hand." (Sagan,1997)
Must see (Sagan nails it.); Carl Sagan's last interview, Charlie Rose.
And of course the "law" that created the world of the computer as we know it today;
Moore's Law, Wikipedia.
The point ultimately is that it's impossible for a population of biological beings to keep pace with a rate of exponential change, for any period of time. Defenses from today's and future attacks will require individuals and families to leverage advances in technology at least as well as the hackers do. It will always be a whack-a-mole game, but going upstream, to the enterprise level of solutions, and then re-orienting these solutions to a non-server environment, just like the hackers and the NSA are doing right now, will provide very effective defenses for anyone to defend their online security and privacy. This happens to be precisely why Total Digital Security was built; to provide enterprise-quality solutions to the individual, the home and family, as well as other small groups and businesses, the defenses necessary for internet security and privacy. Our advantage as users of the internet is that we in ourselves are not of high-value to the hackers. If we take precautionary measures and not be part of large aggregate of data. we have no value to them at all and so are ignored.
Privacy. Word of the Year 2013. Dictionary.com 2013 Word of the Year.
The Potent Brew from Collision of Metadata Collection and Big-Data Software -
The amount of metadata that has been collected by governments, companies, criminals, hackers and others creeps, combined with the power of big-data software presents a new age of cybercrime that is at our footsteps now, today. This powerful brew will manifest itself as ransomware that targets individual users of the internet. There will be massive attacks across broad geographies and the consequences will affect millions. Cyber-risk has truly been democratized and you, your family and small business are now the richest new target that is at the bullseye for the entire hacker community.
"Stalker Economy" here to stay.
Metadata = Surveillance. https://www.schneier.com/blog/archives/2013/09/metadata_equals.html
Do You Have Anything to Worry About?
Awareness and action are crucial. This is the mantra. If you are thinking about not worrying too much about your online security and privacy then I highly encourage reading +Jaron Lanier in the New York Times about Digital Passivity. This is not one to defer or ignore.
Thanks for reading,
Brad
3 Steps to Internet Security, Privacy and Peace of Mind. http://bit.ly/19zxCHa
An offshore email account will vastly reduce the chances of being hacked and be the last email account you will ever need. Why do you want a Swiss-domained email and data storage account?
www.totaldigitalsecurity.com TDS provides best-in-class solutions for individuals, homes and families for protection from cybercrime, online fraud, and the preservation privacy.
Offshore email and data storage for internet security and privacy for you and your family.