3 min read
Let's Talk Mobile
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...
6 min read
 Brad Deflin
:
April 22, 2018
Brad Deflin
:
April 22, 2018

Is your Alexa insisting you call her Olga? When you ask her about the weather at your summer home, does she reply using the word "dacha"? Recently, does she seem to be a little, say, blunt? Perhaps even icy? Well, according to the New York Times, maybe it's because the Russians are in your router!

It's easy to make jokes about the headline, but it's dangerous to miss the message. There are some profound implications imbedded in the first of its kind agreement by the U.S. and U.K. We point these out later. But first, a selection of out-takes from the Times' article on April 16th:
"The sweep and urgency of the statements from both sides of the Atlantic called to mind a computer-age version of a Cold War air raid drill, but asking citizens to upgrade their passwords rather than duck and cover."
"In particular, both governments (the U.S. and U.K.) said, Russians were seeking to exploit ... internet-connected devices around homes and businesses — the so-called internet of things — the kind of thing you and I have in our homes,”
The Times' report continues by quoting Ciaran Martin, chief executive of Britain’s National Cyber Security Center:
"Russia has targeted millions of devices in both countries, often seeking to hack into individual homes or small businesses or to control their routers."
And a quote from Howard Marshall at the FBI's cyber division:
“Once you own the router, you own all the traffic, to include the chance to harvest credentials and passwords. It is a tremendous weapon in the hands of an adversary.”
According to the joint warning, the Russians have methodically targeted routers and connected devices since 2015 and now they "own" and are monitoring millions of them. They're digitally inside private homes, offices and businesses across the U.S. and U.K., and sucking up every bit they can.
So why is the Russian government targeting private homes, offices, and businesses? Why routers? Why would Putin and the KGB care?
Read on because while the answer might be obvious to you, most people still naively claim "nothing to hide" and "who cares?" The fact is that on the front lines of cyberwar, at the intersection of people and the technology they use every day, you could cut the pervading apathy with a knife.
This indifference itself is the biggest problem of all.
After Snowden, Target, Experian, Facebook and the many other large breaches aimed at our personal information, it is clear to some that our everyday stuff is a big deal. Mundane, boring, and irrelevant as our personal information may be on its own accord, in the aggregate and with volumes of associated information, it is exceptionally valuable.
And, unique to information, say as opposed to currency or commodities, the more stuff (data) you have, the more valuable the stuff you already have becomes. This calculus, while relatively new, is increasingly germane to our everyday experience. You can use it's math to determine Facebook's equity valuation, and when explaining how in the digital age, a 25-year old can become a multi-billionaire seemingly overnight.
Information from millions, collected in a persistent and real-time manner (like information extracted from a router), and you're talking not just wealth, but extraordinary power. Hopefully, the image of Facebook CEO Mark Zuckerberg testifying before Congress comes to mind about now because it's a perfect visual for the pervading contrast between Information = Wealth = Power, and the pervading ignorance and apathy.
Information = Wealth = Power. The four words are suddenly interchangeable. Everyone from The Economist Magazine to the futurist Gerd Leonhard is endeavoring to translate the formula that defines the new digital age.
Information is the oil of the digital age.
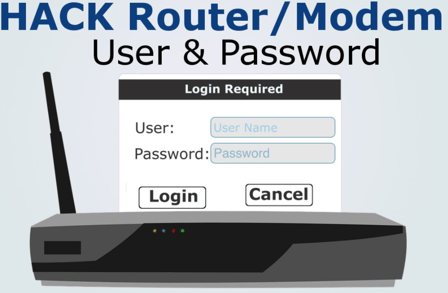
First, in the context of the milestones of the joint warning, we are talking about the routers you own and use every day. These are the boxes where the internet comes in, and your activities and information is distributed out. The router shares your internet with users and devices by way of ethernet cables and Wi-Fi for wireless connections.

We know that to figure anything out you simply "follow the money." If information is money, then eventually you end up at the router. A router is the equivalent of a derrick if we use the oil metaphor - where the rubber hits the road for wealth creation, power, and influence.
The Benefits of Ownership
When another party hacks your router it is said they "own" it. The language of technology has a knack for nailing the essence of a term or concept and that practice applies nicely here.
When your router is "owned" the device becomes a slave and serves a new master - one now in control of all information in and out of the router, as well as all connected devices. In the case of the Russians "owning" our routers, it means everything we do online is monitored, collected, stored, and analyzed. This includes all activities on connected devices; computers, phones, printers, security cameras, and smart TVs.
Yes, even your Alexa serves the Slavs.
More generally, the motivation for the Russians to own our routers is a mix of:
-1.png?width=600&name=Persistent%20access%20to%20millions%20of%20potential%20victims%20to%20create%20disruption%2c%20chaos%2c%20and%20social%20and%20economic%20disorder.%20(1)-1.png)
The Dark Web is full of resources for hacking routers anywhere in the U.S. and U.K. and anyone from the professional criminal to the kid down the street can get them.
Router serial numbers, default passwords, your detailed personal information - whatever they need to hack a router anywhere in the U.S. and U.K - it's all available for a price. Hackers from around the world have been collecting and curating this stuff for years, and now with powerful big data software and algorithms, they can mine and exploit the information for whatever their ultimate agenda may be.
Political, for profit, revenge, harassment, extortion, blackmail, any will or need can be furthered with enough information.
Our routers are all the rage for bad actors everywhere; it's where everything happens, and they're easy to hijack - one at a time, or en masse. The connected planet is one big oil field with built-in gushers everywhere, all available for squatting rights.
As an accommodation to those that don't know how or would rather not bother hacking routers themselves, they can hire a pro to do it for them.
As mentioned earlier here, Russians in our routers should come as no big surprise. Especially when you add what we know about hackers-for-hire.
Here is a look back at some revelations from 2016, "The Rise of the Hacker for Hire."
"Intelligence analysts found that business is booming in underground markets for Russian and other hackers, ...some touting 24/7 customer service and 'free trial attacks' ..."
-Wall Street Journal, April 5th, 2016
The main point? Everyone wants your stuff. Don't let them have it.
Learn to think critically about your personal information and online activities.
Stop making it so easy for them, and start acting differently about your stake in the new era of wealth, power, and the security of your home, family, and business.
If you own assets, transact anything online, or if anyone depends on you for influence or advice, you are increasingly in the queue for a bad actor from somewhere to get the better of you. Anyone with ambition for wealth and power wants your stuff. Whether they're from the Kremlin, KGB, or Kansas.
First, no reason to panic.
If you take some precautions now, you are ahead of the game. And, you're in a good spot to keep your edge with some basic measures for the future.
Second, start to treat your personal and professional information as your god-given oil fields, and protect the gushing of your drills (routers) from siphoning - by anybody. Nation states, big tech, cybercriminals, competitors, kid down the street, ... it's time to keep them all out, and take back control of your most precious and gushing commodity.
As we explained, the on-ramp and port-of-entry to your digital self is your router. Whether at home, office, or business, it's the gate where your every bit passes, and when hacked, is collected and controlled by a third party.
Here are three "must do" items for your home, office, and business routers:
For a list of guides and password references specific to your router and network, click "Router Resources" below:
Enterprise-grade Router Security
Total Digital Security uniquely makes enterprise-grade IT security solutions accessible, affordable and easy to use. And router security is an excellent example of the innovative and effective answers the cybersecurity industry brings forth today.
Our Router Network Security solution is an IT security department in the cloud that manages all aspects of router and network security, including Wi-Fi. The service also protects and secures ALL devices connected to your network. It's a comprehensive solution that works in real-time, all the time, with the latest threat intelligence and attack defenses.
We give you the "appliance" free, as part of the service. It's plug-and-play, set-it-and-forget-it easy. This is empowering and enabling technology, and you can learn more about it here:
Here's an illustration of a typical installation for Router Network Security, with the appliance in the middle.:
Want to learn more? Need help?
Small-businesses, individuals, homes, offices, and families; we help you learn, protect, and succeed in the new age of risk.
Contact us for more information about any of our products and services.

3 min read
We spend a great deal of time thinking about protecting our homes, our computers, and our networks. Yet the single most important device in our...

5 min read
A massive cyberattack made headlines — and the weapons it used might be sitting in your home or office right now.

5 min read
In our last post, we introduced the three primary attack surfaces every family needs to understand: email, devices, and networks. Today we're going...