What We Do: 1-Minute Animation
The elevator speech - an effective expression of your value proposition stated as quickly and succinctly as possible. It's not always easy to...

Cyber crime has become the predominant risk we face as a society today, and when you consider the longterm mega-trends driving change; it's clear we are still in the early innings compared to what is to come. A massive storm of crime is immediately ahead, expected to last for at least the next five to ten years, and most are entirely unprepared - especially considering the potentially life-altering consequences at stake.
Total Digital Security was formed in 2013 to seek the best internet security technology on the planet and make it accessible, easy to use, and highly affordable to most anyone. After three years helping our customers to build new levels of privacy and information security, we have never been more committed to our original mission and cause.

Cyber Crime - The Crime of the Future
There is no crime more profitable than cyber crime and without a face, nor a weapon; it can be perpetrated from anywhere. There is little risk of getting caught and the upside; the ROI, or return on investment, makes traditional crimes pale in comparison.
According to Trustwave, the Chicago-based information security company that serves over 3 million customers around the world, returns can easily top 1,425% in just 30 days.
One, single successful attack can pay for a career in crime.
The irresistible lure of big, easy money is driving every major cartel and minor street criminal to the game, and the cycle will take years to wash itself out.
Cyber attacks against end-users can generate an ROI of 1,425% in just 30 days. Trustwave, June 2015, based on a study of activities in 2014.
The quote above by Trustwave uses the term "end-user", which is another way of saying you, me, our employees, and our family members.
Have you noticed the target of attacks on large companies and the U.S. Government are aimed at stealing personal information? The preponderance of cyber crime today is aimed at individuals and small groups.
Why?
Because it's easy, it can be done in volume and is easily scaled to score very large sums of money, and the chances of getting caught are exceedingly low. This is the future of crime. For the full report by Trustwave, click here.
A massive, 3-5 year storm of cyber crime lays ahead, and most are entirely unprepared for what is to come. Total Digital Security, Dec. 2015
The Cyber Security Industry
For 20+ years the cyber security industry has lagged advances in other technologies. The market was limited in scale and potential for profit, and a handful of companies dominated over emerging innovators that periodically emerged to threaten their gravy train.
In 2013, everything changed.
Snowden, Target, and new HIPAA laws brought two powerful forces to play: regulatory pressures and broad consumer awareness.
New Regulatory Forces and Broad Consumer Awareness Drive Innovation.
The twin forces of regulatory compliance in privacy and information security and a newly aware consumer base has vastly increased the market's size and the potential for economic success in cyber security. This, coupled with a strong funding environment, has just in the last few years attracted smart, entrepreneurial capital and talent to the industry.
But today, to the benefit of the consumer, innovation in the cyber security industry is flourishing and products will continue to improve rapidly over the next several years.
Now, for our favorite chart of 2015 which we call "A Picture of Innovation"
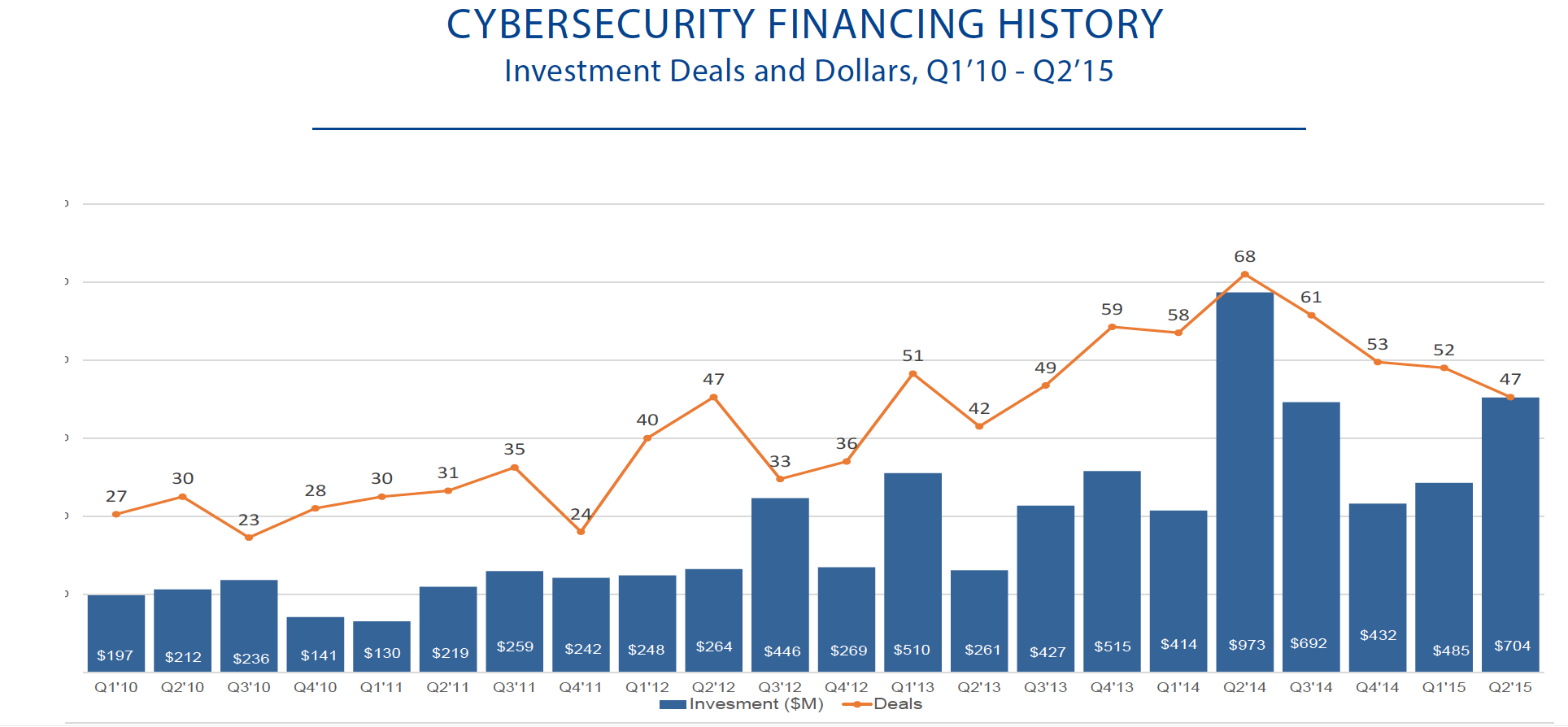
In 5 years, $7.3B invested over 1028 deals, 2014 marked a record year for deal activity and funding for cybersecurity. CB Insights - Cybersecurity Financing and M&A Trends, 2015.
The chart illustrates innovation. Finally, after years of stagnation in the cybersecurity industry, new products and solutions are emerging, and they are far better than before, much easier to use, and highly affordable.
Consistent with all digital technologies, now we can plan on better, faster, easier, and cheaper from the cybersecurity industry for many years to come.
Total Digital Security was formed in 2013 to bring the best cyber security technology available to those that need it most; the everyday users of the internet that own smartphones and computers.
When you break it down, Total Digital Security does just four things:
1) We analyze the threat environment - What's happening in online crime? How are criminals, terrorists, hackers, creeps and the rest, exploiting the internet today? And, how those risks threaten our customers?
2) We follow innovation in the cybersecurity industry - What's being done to defend from the threats and who is building it? Which products and services are most suitable for protecting our customers?
3) We match our customers with the technology - Which technology will keep our customers and their unique needs optimally positioned for protection? How do we fully leverage the rapid advances in technology for the benefit of protecting our customers?
4) We make it easy for our customers - What will make it easier for the customer? How can we make an eco-sytem of cybersecurity as seamless and ubiquitous as possible? What can we do to better inform, educate, coach and advise our customers?
These four things are done systematically with discipline and detail by asking ourselves the 10 questions above, every day.
We believe cyber security is a service, not a product you can buy and sell. It's a virtuous cycle of vigilance, assessment, adjustment, and optimization - in conjunction with a relationship-based model for user (customer) relations.
Total Digital Security's mission is to be our customers' trusted partner for all things related to their cyber risk; the threats they face, the technology that will protect them, and the counsel they need to stay smart, secure and safe.
The threats will increase and evolve with greater sophistication, but so will the solutions - it's the nature of technology and can work to your advantage. We wrote more about it here:
"Managing Change in the Digital Age."
Remarkable progress across all of digital technology is contributing to the new generation of innovation in cyber security products and services. Examples include:
These are just some of the examples of advances that are significantly altering the cyber security landscape.
These new technologies in cybersecurity are "smart", automatically updated, and constantly optimized for efficacy in the ever-changing threat environment.
We help our customers use this technology to create a cyber-secure environment that works everywhere, all of the time, and with little or no input required of themselves.
Our approach is according to "The Four Fundamentals of Cyber Security". We apply our process to solve for each of the Fundamentals, according to the unique needs of the customer.
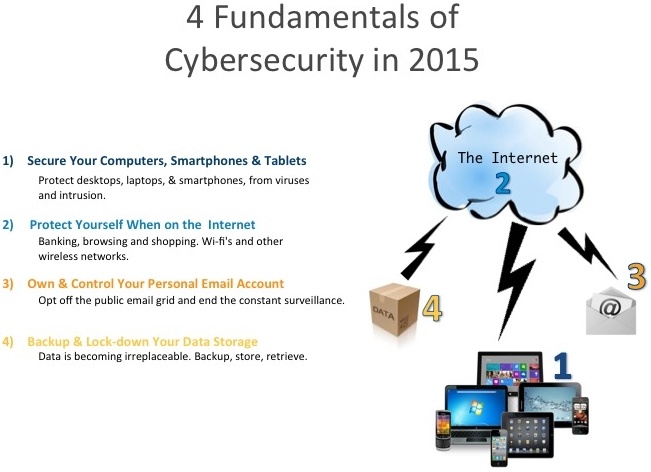
We spoke at the Association of Financial Professionals Annual Corporate Treasures Conference earlier this year and wrote this about "The Four Fundamentals of Cyber Security."
Our Solutions to each of The Four Fundamentals
Solving for each of the four fundamentals creates an eco-system of cyber security that is highly effective at dramatically reducing one's risk to the internet and cyber crime.
Fundamental #1 - Protect Your Devices. Your phone, computer, laptop, pad, - whatever you own and use to access the internet needs to be protected from viruses, external intruders, data loss, malicious apps, and a host of other threats that daily barrage our technology.
![]() Solution #1 - Each device our customers own is monitored and managed independently with real-time intelligence and defenses, quickly and automatically.
Solution #1 - Each device our customers own is monitored and managed independently with real-time intelligence and defenses, quickly and automatically.
For more about how this highly effective technology works, and the service we recommend, please click here.
Fundamental #2 - Protect When Connected to the Internet. When you are on the internet, browsing, banking, shopping, using passwords, and everything else you do that is transmitted over the internet should be encrypted - made invisible to the outside.
![]() Solution #2 - We install a commercial-grade VPN, or Virtual Private Network, on each device a customer owns. A VPN automatically encrypts all internet activities and "tunnels" your traffic off of the public internet "grid".
Solution #2 - We install a commercial-grade VPN, or Virtual Private Network, on each device a customer owns. A VPN automatically encrypts all internet activities and "tunnels" your traffic off of the public internet "grid".
For more detail about VPN's and the service we recommend, click here.
Fundamental #3 - Secure Your Email. Email has become an integral part to most all we do. Public, or "free" email services hemorrage your information to 3rd parties and inadvertently to criminals and creeps too. Use private and secure email services that do not resell your personal information and are not used as "honey-pots" for hackers and cyber-criminals to monitor your activities.
![]() Solution #3 - We create private email domains for our customers and use business-class services that include spam controls and filters to keep the maliscious actors out.
Solution #3 - We create private email domains for our customers and use business-class services that include spam controls and filters to keep the maliscious actors out.
For more on how we "privatize" email and significantly decrease our customers loss of personal information to increase overall security, click here.
Fundamental #4 - Protect Your Sensitive Data. Keep the important stuff safe - legal documents, tax returns, healthcare records, identification information, passwords - all should be kept especially secure from theft and loss.
![]() Solution #4 - Online digital vaults for sensitive and treasured electronic files are the safe deposit box of the future. Digital vaults are exceptionally secure, off the cloud (but feels cloud-like), safe from fire and other natural disasters, and protected from the daily attacks on our privacy and personal information. These vaults also include inheritance and beneficiary rights that are increasingly useful for easing the estate settlement process, and avoiding probate.
Solution #4 - Online digital vaults for sensitive and treasured electronic files are the safe deposit box of the future. Digital vaults are exceptionally secure, off the cloud (but feels cloud-like), safe from fire and other natural disasters, and protected from the daily attacks on our privacy and personal information. These vaults also include inheritance and beneficiary rights that are increasingly useful for easing the estate settlement process, and avoiding probate.
For further detail about digital vaults and our preferred provider, please click here.
Each of these solutions represents the best science available in the cybersecurity industry today - Fortune 500 quality and typically used exclusively by large institutions and "mission critical" environments. Total Digital Security uniquely brings these products to the rest of us, and we will continue to find better, faster, easier, and cheaper protection technologies to bring them to bear for our customers.
Our customers are typically neglected by the IT security industry. Most companies in the business focus on selling to large organizations and consider our target markets too small and fragmented for their purposes.
Since 2013, Total Digital Security has uniquely focused on these smaller markets, informing them of products and technologies they otherwise may not be aware of, but are highly capable of suiting their needs and significantly reducing their risk.
Our customers include:
Individuals and families.
Home and remote offices.
Professional practices and family offices.
Trusted advisors - real estate agents, consultants, deal teams.
Nonprofit organizations.
Small businesses and regulated PCI and HIPAA operations.
In many cases, our customers use multiple devices - computers, pads, and phones - and the internet has become an important part of their lives. They recognize that personally and professionally, everyday life is more connected online to the internet and they care about the privacy, security, and personal safety of those around them.
Our customers do not want more hardware, complications, or contracts, and they want the best value available at any given time.
*** A note on individuals, homes, and families - Total Digital Security is a leader in the application of advanced cybersecurity principals to the individual user and their devices. Individuals, homes, and families are becoming exceedingly vulnerable to cyber risk and without protection, are exposed to needless risks that can have deep, life-altering consequences. We bring the best defenses available to our markets and are deeply committed to our focus on the home and family.

Total Digital Security was created from need. Leading an engaged, productive, and informed life today requires digital technology, and using the internet can enhance and contribute to the quality of one's overall experience.
To operate safely and successfully with technology, individuals must recognize personal responsibility for the risks and take action to protect from them. Governments, militaries, and corporations clearly cannot and will not protect - it is up to us.
With the internet, the world's knowledge and information are at our fingertips - fear and risk should not stand in the way."
Brad Deflin, Dec. 2015.
Total Digital Security
The elevator speech - an effective expression of your value proposition stated as quickly and succinctly as possible. It's not always easy to...

Since 2013, Total Digital Security has been serving individuals, families, professional practices, and small businesses with advanced resources and...
Brad Deflin tells the Total Digital Security story in this Q&A from May 16th, 2024.
Congrats! You've just become a magician. This is the do-it-all module where you can let your creativity run wild. The best part is that it's just going to keep getting more and more awesome over time.