Top risks for early 2016, and a look at some favorite take-aways from 2015.
Hi there,
So, as we finish 2015 we start 2016 a little early with the first edition of our newsletter; "The Cyber Advisor."
We'll endeavor to inform, educate, and provide practical information and tools for managing and mitigating cyber risk as it is rapidly becoming the predominant risk in our every day lives.
You can easily "unsubscribe" from the link at the bottom of the page, but I hope you will give us a try and will find value to reading our weekly report. As always, suggestions and input are welcome, and "sharing" with others is highly appreciated.
Start 2016 from Strength.
Hackers and cyber criminals are looking for a banner year in 2016. In this week's letter, we'll begin by informing you of your top-risks for the start of the new year, and solutions to defend.
In the early weeks and months of 2016, we expect the IRS Tax Refund Scam, and Apple and PayPal email phishing to be the top risks for individuals, families, and employees.
Tax Refund Scam
I n 2016, the IRS and the states expect the tax-refund scam to victimize more individuals and families than ever.Take matters into your own hands by getting an IP PIN from the IRS. Unbelievably, the online service is out of commission until January - another reason to take individual responsibility for protecting ourselves - I suggest using their form 14039.
n 2016, the IRS and the states expect the tax-refund scam to victimize more individuals and families than ever.Take matters into your own hands by getting an IP PIN from the IRS. Unbelievably, the online service is out of commission until January - another reason to take individual responsibility for protecting ourselves - I suggest using their form 14039.
Key Points:
-
The IRS will never use email to initiate requests for financial information.
-
A credit "freeze" works better than credit "monitoring".
-
Get an IP PIN by filing form 14039 with snail-mail to reduce the risk of PIN theft.
Apple Target Practice
 Be on the lookout for an email phishing scam that portends to be from Apple Support. With a ton of Apple devices sold this Christmas, the email is aimed at new users warning them of an Apple ID account suspension. The email includes a "Verify Now" button that gives the bad guys control of your computer and information. When it comes to email; if in doubt, DELETE it out!
Be on the lookout for an email phishing scam that portends to be from Apple Support. With a ton of Apple devices sold this Christmas, the email is aimed at new users warning them of an Apple ID account suspension. The email includes a "Verify Now" button that gives the bad guys control of your computer and information. When it comes to email; if in doubt, DELETE it out!
PayPal Phishing

 The PayPal phishing exploits we are seeing over the holidays are just one example of many, including Amazon, FedEx and UPS, Walmart, Costco, and the popular Apple version we discuss above. The PayPal and Apple versions seem to be the most prevalent over the past week, or so. The email requests account information verification for delivery or payment purposes and, of course, is just a scam and the rule applies: if in doubt, delete it out.
The PayPal phishing exploits we are seeing over the holidays are just one example of many, including Amazon, FedEx and UPS, Walmart, Costco, and the popular Apple version we discuss above. The PayPal and Apple versions seem to be the most prevalent over the past week, or so. The email requests account information verification for delivery or payment purposes and, of course, is just a scam and the rule applies: if in doubt, delete it out.
Our Newest Products for 2016
In the first quarter of 2016, we will introduce two new products to our line-up of "best-in-class" solutions - a password manager, and a new VPN service.
 We've hesitated to sell password managers in the past because they were less than user-friendly and clunky to use. Personally, I have used and advocated LastPass for years, and now I think they are clearly first in their field and making all the right moves for their consumers.
We've hesitated to sell password managers in the past because they were less than user-friendly and clunky to use. Personally, I have used and advocated LastPass for years, and now I think they are clearly first in their field and making all the right moves for their consumers.
 We will offer PureVPN as an alternative to F-Secure's Freedome, which we will continue to offer. Unlike Freedome, PureVPN is compatible across all devices and platforms, and a single license can be used on up to five connections, so it's more affordable for some users. Freedome, though more narrow in it's compatibility, is an enterprise-level service that includes remote Lock, Wipe, and Erase features.
We will offer PureVPN as an alternative to F-Secure's Freedome, which we will continue to offer. Unlike Freedome, PureVPN is compatible across all devices and platforms, and a single license can be used on up to five connections, so it's more affordable for some users. Freedome, though more narrow in it's compatibility, is an enterprise-level service that includes remote Lock, Wipe, and Erase features.
2015 - A Look Back at Some Favorites for the Year.
Our Favorite Article of 2015
 Maybe we think Harvard Business Review's "Cybersecurity's Human Factor: Lessons From the Pentagon" is so great because it's consistent with how we see the world. Cybersecurity today requires individual responsibility - it's up to us and reckless to think someone will take care of things for you. 2016 may well mark the last reasonable chance you have to take initiative and preemptively avoid the losses and inconveniences of a breach.
Maybe we think Harvard Business Review's "Cybersecurity's Human Factor: Lessons From the Pentagon" is so great because it's consistent with how we see the world. Cybersecurity today requires individual responsibility - it's up to us and reckless to think someone will take care of things for you. 2016 may well mark the last reasonable chance you have to take initiative and preemptively avoid the losses and inconveniences of a breach.
Our Favorite Chart of 2015
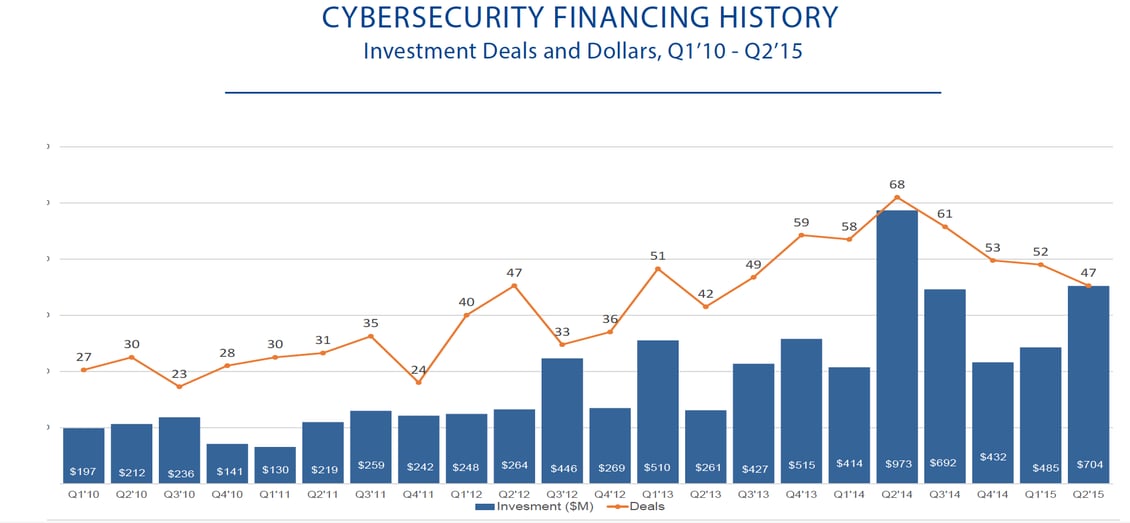
Cybersecurity technology is good, and getting better quickly as a result of a massive increase in capital spending in the IT security industry.
A picture of innovation:
And, this money is being deployed by some of the most innovative and entrepreneurial minds on the planet, including:
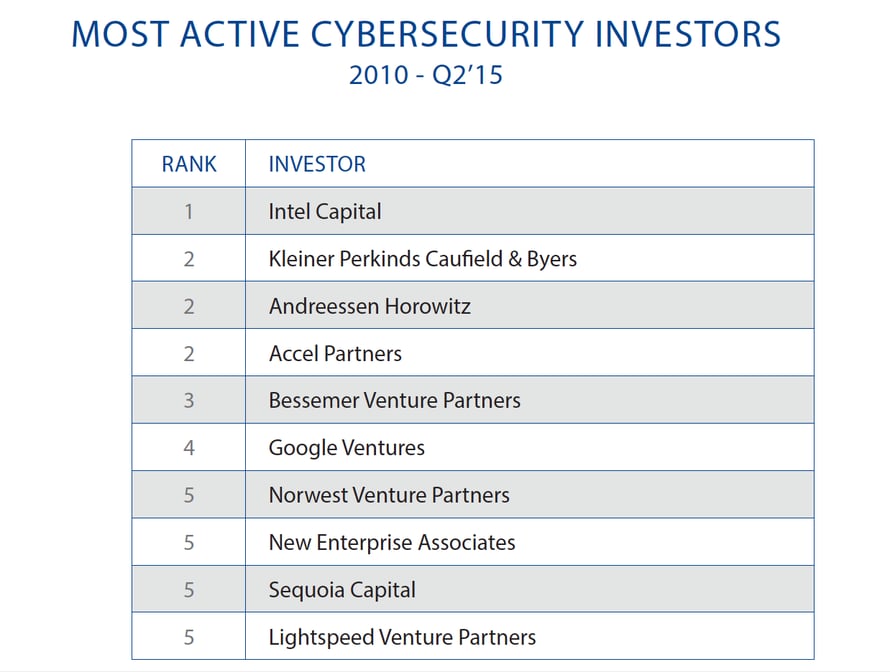
These two charts by CB Insights paint a beautiful picture for us because it's our job at TDS to monitor the industry and bring you the best the industry has to offer for your particular needs. Uniquely, we find powerful solutions that are only being sold to Fortune 500 sized organizations and make them available and easy to use for you and your environments.
#1 Top Post of 2015
Personally, I would have never guessed our top post for 2016 in terms of views and engagement would be "Ransomware - 4 Things You Must Know." Maybe it's the imperative nature of the title that got your attention, perhaps combined with a list of "4 Things" it gave the impression that important truths were just a click away. Or, perhaps it was my bold prediction that 10's of millions of people will be victims in the few short years ahead.
Whatever, we're just pleased that as a result of the blog's success, more people have an understanding of the word and perhaps a higher level of awareness that will matter one day. One thing you can count on, "ransomware" will be a household word soon as criminal cartels will steal hundreds of millions, potentially billions, from everyday people - a couple of hundred dollars at a time.
pleased that as a result of the blog's success, more people have an understanding of the word and perhaps a higher level of awareness that will matter one day. One thing you can count on, "ransomware" will be a household word soon as criminal cartels will steal hundreds of millions, potentially billions, from everyday people - a couple of hundred dollars at a time.
"We predict ransomware will victimize ten's of millions of individuals before it's over and the easy money is exhausted."
In 2016 we can expect capital investment in the cybersecurity industry to advance protective technology and bring substantial improvements in efficacy, ease-of-use, and price - and we will inform our customers and readers every step of the way.
We extend our best wishes to all for the New Year, and thanks for reading.


What We Do, How We Do It, Who We Do It For.